Account Status Reports
26 ReportsAbout Account Status Reports
Account Status Reports provide critical visibility into the state and lifecycle of user accounts in your Active Directory. Track enabled/disabled accounts, locked users, expiration settings, security configurations, and account changes for comprehensive access management and security compliance.
Monitor account security and access control
Track account creation, changes, and expiration
Identify locked and disabled accounts quickly
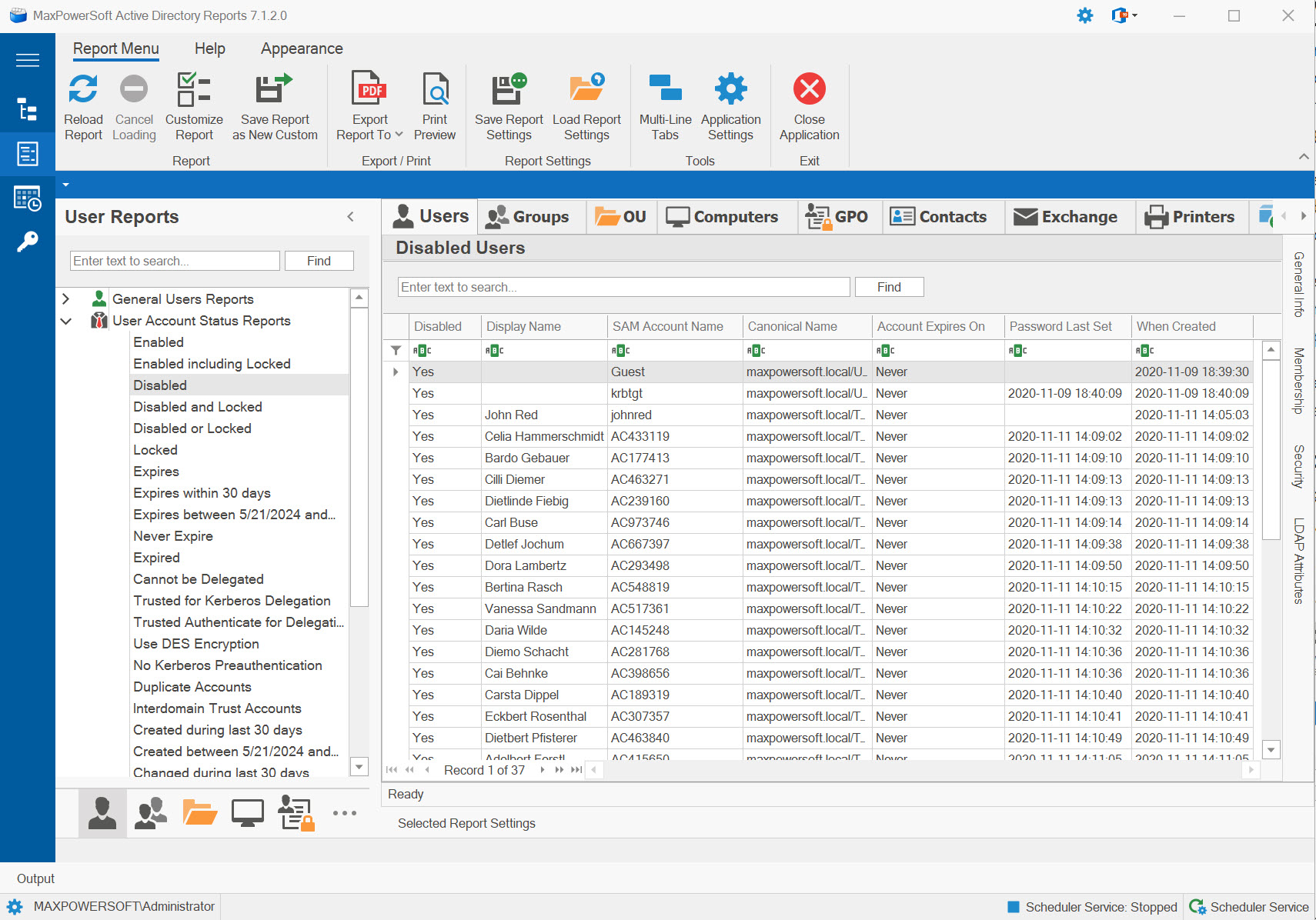
Example: Account Status Reports in AD Reports
- → Enabled User Accounts
- → Enabled Including Locked
- → Disabled User Accounts
- → Disabled and Locked
- → Disabled or Locked
- → Locked User Accounts
- → Accounts Set to Expire
- → Expiring Within XX Days
- → Expiring Between Dates
- → Accounts Never Expire
- → Expired Accounts
- → Cannot Be Delegated
- → Trusted for Kerberos Delegation
- → Trusted Authenticate for Delegation
- → Accounts with DES Encryption
- → No Kerberos Preauthentication
- → Duplicate Accounts
- → Interdomain Trust Accounts
- → Created During Last XX Days
- → Created Between Dates
- → Changed During Last XX Days
- → Changed Between Dates
- → Deleted User Accounts
- → Deleted During Last XX Days
- → Deleted Between Dates
- → Service Accounts
Available Reports
Enabled User Accounts
Lists all active user accounts that are neither disabled nor locked, representing users who currently have full access to network resources and can authenticate successfully.
Use Cases
- Audit currently active user accounts
- Verify user access permissions
- Generate active user inventory
- Baseline for security assessments
Key Information
- User account names and UPNs
- Account status (enabled/unlocked)
- Last logon timestamps
- Department and location
- Account creation dates
Enabled Including Locked User Accounts
Shows all enabled accounts including those that are temporarily locked out due to failed login attempts. Helps identify accounts that need attention but aren't permanently disabled.
Use Cases
- Identify accounts needing unlock
- Monitor account lockout patterns
- Help desk support requests
- Security incident investigation
Key Information
- Enabled and locked accounts
- Lockout timestamps
- Bad password attempts
- Lockout duration remaining
- User contact information
Disabled User Accounts
Lists all user accounts that have been administratively disabled, preventing authentication and resource access. Typically used for terminated employees, suspended accounts, or temporary access restrictions.
Use Cases
- Audit disabled accounts for cleanup
- Verify terminated employee processing
- Identify accounts for deletion
- Compliance and security auditing
Key Information
- Disabled account names
- When account was disabled
- Last logon before disable
- Account age and history
- Manager and department info
Disabled and Locked User Accounts
Identifies accounts that are both administratively disabled AND locked out, representing accounts with maximum access restrictions. Often indicates security concerns or accounts pending deletion.
Use Cases
- Identify accounts with dual restrictions
- Security incident cleanup
- Verify terminated user lockdown
- Prioritize accounts for deletion
Key Information
- Both disabled and locked status
- Timeline of restrictions
- Reason for disable (if documented)
- Last activity before lockdown
- Associated security events
Disabled or Locked User Accounts
Comprehensive list of all accounts with any access restriction - either disabled, locked, or both. Provides complete visibility into non-functional accounts requiring attention.
Use Cases
- Complete restricted accounts inventory
- Help desk queue management
- Access problem troubleshooting
- Comprehensive security audit
Key Information
- All non-functional accounts
- Type of restriction (disabled/locked/both)
- Restriction duration
- Impact on users
- Resolution priority
Locked User Accounts
Shows all accounts locked out due to failed authentication attempts, regardless of enabled/disabled status. Critical for help desk support and security monitoring of authentication failures.
Use Cases
- Monitor authentication failures
- Help desk unlock requests
- Detect brute force attacks
- User training opportunities
Key Information
- Locked account names
- Lockout timestamp
- Number of failed attempts
- Originating computer/IP
- Auto-unlock timeframe
Accounts Set to Expire
Lists all accounts configured with an expiration date, typically used for temporary workers, contractors, or time-limited access. Essential for managing temporary account lifecycles.
Use Cases
- Track temporary account lifecycles
- Contractor access management
- Project-based access control
- Compliance with time-limited access
Key Information
- Account expiration dates
- Days until expiration
- Account type (contractor, temp, etc.)
- Responsible manager
- Renewal requirements
Accounts Expiring Within XX Days
Proactive report showing accounts expiring within a customizable timeframe. Allows you to plan renewals or terminations and notify stakeholders before access is automatically removed.
Use Cases
- Proactive expiration notifications
- Renewal processing workflow
- Manager alerts for contractors
- Access continuity planning
Key Information
- Exact expiration date/time
- Days remaining before expiration
- User contact and manager
- Account purpose/project
- Renewal history
Accounts Expiring Between Dates
Filter accounts expiring within a specific date range for targeted review and planning.
Use Cases
- Quarterly expiration reviews
- Project end-date planning
- Fiscal year-end processing
- Bulk renewal workflows
Key Information
- Custom date range filtering
- Expiration dates within range
- Account details and managers
- Business justification
- Renewal status tracking
Accounts Never Expire
Lists permanent accounts configured to never expire.
Use Cases
- Verify permanent employee accounts
- Audit service account settings
- Identify misconfigurations
- Compliance policy validation
Key Information
- Never-expire configured accounts
- Account types (user, service, etc.)
- Employment status verification
- Last logon activity
- Account age
Expired Accounts
Shows accounts that have already expired and can no longer authenticate.
Use Cases
- Identify accounts for deletion
- Process expired contractors
- Clean up stale accounts
- Security posture improvement
Key Information
- Expiration dates (past)
- Days since expiration
- Last activity before expiration
- Account owner/manager
- Data retention requirements
Cannot Be Delegated
Lists sensitive accounts marked as "Account is sensitive and cannot be delegated" to prevent Kerberos delegation.
Use Cases
- Audit privileged account protection
- Security compliance verification
- Prevent delegation attacks
- Identify sensitive accounts
Key Information
- Non-delegatable accounts
- Account privilege levels
- Group memberships
- Security requirements
- Delegation restrictions
Trusted for Kerberos Delegation
Shows accounts trusted for unconstrained Kerberos delegation, allowing them to impersonate users.
Use Cases
- Audit delegation permissions
- Security risk assessment
- Service account validation
- Reduce attack surface
Key Information
- Accounts with delegation trust
- Services using delegation
- Security implications
- Delegation type (unconstrained)
- Risk assessment
Trusted to Authenticate for Delegation
Lists accounts configured for protocol transition.
Use Cases
- Audit protocol transition settings
- Service account security review
- Application authentication analysis
- Delegation compliance checking
Key Information
- Protocol transition accounts
- Allowed delegation targets
- Application associations
- Security configuration
- Constrained delegation settings
Accounts with DES Encryption
Identifies accounts restricted to using weak DES encryption.
Use Cases
- Identify weak encryption usage
- Security vulnerability assessment
- Legacy application identification
- Upgrade planning for modern encryption
Key Information
- Accounts using DES
- Encryption type restrictions
- Associated applications
- Security risk level
- Upgrade requirements
No Kerberos Preauthentication
Shows accounts vulnerable to AS-REP roasting attacks.
Use Cases
- Identify AS-REP roasting vulnerabilities
- Security hardening initiatives
- Attack surface reduction
- Compliance remediation
Key Information
- Accounts without preauth
- Attack vulnerability status
- Reason for exception (if any)
- Account privilege level
- Remediation priority
Duplicate Accounts
Lists local user accounts whose primary account is registered in a different domain.
Use Cases
- Identify local user accounts
- Domain migration cleanup
- Access boundary verification
- Trust relationship auditing
Key Information
- Local account names
- Primary domain registration
- Access scope limitations
- Trust relationships
- Account purpose
Interdomain Trust Accounts
Shows accounts with permissions for complex multi-domain trust configurations.
Use Cases
- Audit trust relationships
- Multi-domain architecture review
- Security boundary verification
- Complex trust configurations
Key Information
- Trust account names
- Domain trust paths
- Trust types and directions
- Security implications
- Trust validation status
Accounts Created During Last XX Days
Tracks recently created accounts within a customizable timeframe.
Use Cases
- Monitor new account creation
- Onboarding process verification
- Detect unauthorized accounts
- New hire tracking
Key Information
- Creation date and time
- Created by (administrator)
- Account type and purpose
- Initial group memberships
- Manager and department
Accounts Created Between Specified Dates
Filter account creation by specific date range for historical analysis.
Use Cases
- Historical account creation analysis
- Audit period compliance
- Hiring trend analysis
- Security incident investigation
Key Information
- Creation dates within range
- Accounts created in period
- Creation patterns and trends
- Responsible administrators
- Onboarding metrics
Accounts Changed During Last XX Days
Tracks accounts with modified attributes within a customizable timeframe.
Use Cases
- Monitor unauthorized changes
- Change management auditing
- Troubleshoot account issues
- Security event correlation
Key Information
- Last modification timestamp
- Modified by (administrator)
- Account names changed
- Change frequency
- Attribute modifications
Accounts Changed Between Specified Dates
Filter account modifications by specific date range.
Use Cases
- Audit period change tracking
- Security incident investigation
- Change management compliance
- Administrator activity review
Key Information
- Change dates within range
- Modification patterns
- Administrator responsible
- Change volume metrics
- Impact assessment
Deleted User Accounts
Shows all deleted user accounts still in the tombstone or recycle bin state.
Use Cases
- Recover accidentally deleted accounts
- Audit account deletions
- Track account lifecycle
- Offboarding verification
Key Information
- Deletion date and time
- Deleted by (administrator)
- Account name (if recoverable)
- Days until permanent deletion
- Recycle bin vs tombstone
Deleted User Accounts During Last XX Days
Tracks recently deleted accounts within a customizable timeframe.
Use Cases
- Monitor recent deletions
- Catch accidental deletions early
- Offboarding compliance
- Quick recovery operations
Key Information
- Recent deletion timestamps
- Responsible administrators
- Account details before deletion
- Recovery options available
- Termination documentation
Deleted User Accounts Between Specified Dates
Filter deleted accounts by specific date range for historical analysis.
Use Cases
- Audit period deletion review
- Offboarding metrics analysis
- Historical data recovery
- Compliance documentation
Key Information
- Deletion dates within range
- Number of accounts deleted
- Deletion patterns and trends
- Administrators responsible
- Recovery feasibility
Service Accounts
Service accounts including delegation-trusted users, Managed Service Accounts (MSAs), and Group Managed Service Accounts (gMSAs). Provides a consolidated view of all accounts used to run services and automated processes.
Use Cases
- Inventory all service accounts
- Identify delegation-trusted accounts
- Audit MSA and gMSA usage
- Security review of privileged services
Key Information
- Account name and type (user/MSA/gMSA)
- Delegation trust settings
- Account status (enabled/disabled)
- Last logon and password change
Related Reports
Explore other user report categories for additional insights:
See These Reports in Action
Try AD Reports free for 14 days — run any of these reports on your own Active Directory.
Download Free Trial View All Features