General Computer Reports
20 ReportsAbout General Computer Reports
General Computer Reports provide comprehensive insights into all computer objects in Active Directory including workstations, servers, and domain controllers. Track managed systems, account status, trust relationships, and delegation settings. Essential for maintaining inventory and security of your computer infrastructure.
Complete computer tracking
Track servers & DCs
Monitor trust & delegation
About AD Computer Objects
Computer objects in Active Directory represent physical or virtual machines:
- Computer Name: Unique network identifier
- Trust Account: Secure relationship with domain
- Group Membership: Determines resource access and GPO application
- Security Principal: Can be granted permissions to resources
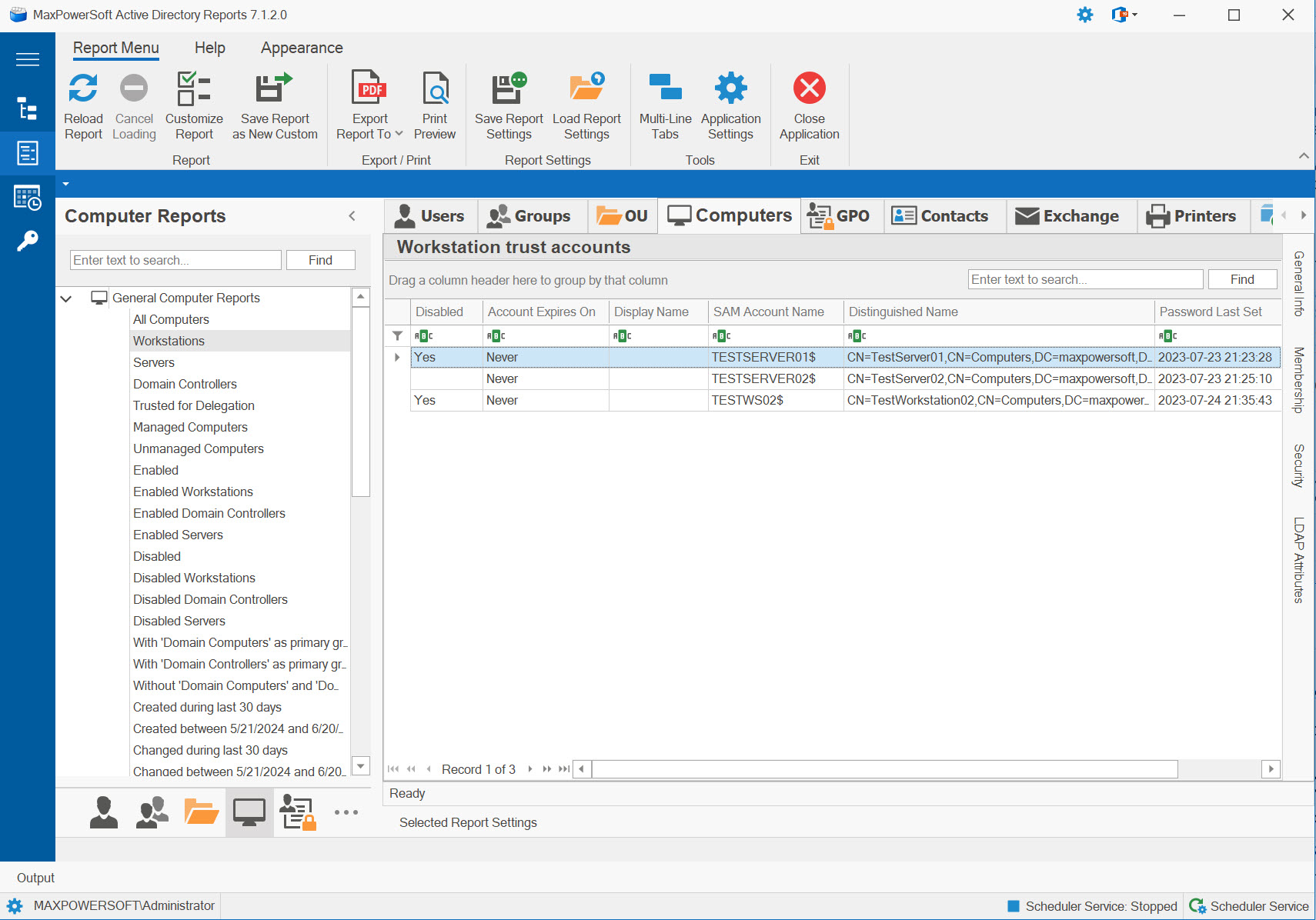
Example: General Computer Reports
Available Reports
All Computer Accounts
Comprehensive inventory of all computer objects in the domain - workstations, servers, and domain controllers.
Use Cases
- Complete device inventory
- Asset management baseline
- Total computer count
- Infrastructure overview
Key Information
- All domain computers
- Computer names and DNS names
- Operating systems
- OU locations
- Account status (enabled/disabled)
Workstation Trust Accounts
Lists all workstation computers - desktops and laptops used by end users.
Use Cases
- Endpoint device inventory
- Workstation-specific policies
- Desktop management
- User device tracking
Key Information
- Workstation computers only
- Excludes servers and DCs
- User-facing devices
- Desktop & laptop systems
- End-user machines
Server Trust Accounts
Shows all member servers - application servers, file servers, web servers, etc. (excludes domain controllers).
Use Cases
- Server infrastructure inventory
- Member server tracking
- Server-specific GPO targeting
- Critical system identification
Key Information
- Member servers only
- Excludes domain controllers
- Application/file/web servers
- Production infrastructure
- Server OS versions
Domain Controllers
Lists all domain controllers - critical infrastructure servers hosting Active Directory.
Use Cases
- AD infrastructure audit
- DC health monitoring
- Replication topology verification
- Critical system tracking
Key Information
- All domain controllers
- DC names and sites
- FSMO role holders
- Server versions
- Most critical AD servers
Computers Trusted for Kerberos Delegation
Identifies computers configured for Kerberos delegation - can act on behalf of users to access resources.
Use Cases
- Security audit for delegation
- Identify privileged computers
- Double-hop authentication setup
- Service account troubleshooting
Key Information
- Delegation-enabled computers
- Unconstrained vs constrained
- Allowed services (if constrained)
- Security implications
- Potential privilege escalation risk
Managed Computer Accounts
Shows computers with assigned managers - enables ownership and accountability.
Use Cases
- Ownership accountability
- Asset assignment tracking
- Manager delegation verification
- Device responsibility
Key Information
- Computers with managers assigned
- Manager names and contacts
- Ownership accountability
- Department/team assignment
- Asset responsibility
Unmanaged Computer Accounts
Identifies computers without assigned managers - no clear ownership or accountability.
Use Cases
- Find unassigned computers
- Identify orphaned devices
- Ownership gap identification
- Manager assignment planning
Key Information
- Computers without managers
- No assigned ownership
- Accountability gaps
- Potentially orphaned
- Assignment candidates
Enabled Computer Accounts
Shows all enabled computers - active accounts that can authenticate and access resources.
Use Cases
- Active device inventory
- Production computer count
- Policy application targets
- License planning
Key Information
- All enabled computers
- Can authenticate to domain
- Active accounts
- Production systems
- Policy targets
Enabled Workstations
Lists only enabled workstation computers - active user-facing devices.
Use Cases
- Active endpoint count
- User device inventory
- Endpoint protection licensing
- Desktop management scope
Key Information
- Active workstations only
- Enabled desktops & laptops
- Production user devices
- End-user machine count
- Endpoint scope
Enabled Servers
Shows only enabled servers - active infrastructure and application servers.
Use Cases
- Active server inventory
- Production infrastructure count
- Server licensing planning
- Critical system tracking
Key Information
- Active servers only
- Enabled infrastructure
- Production server count
- Application/file/web servers
- Critical systems
Disabled Computer Accounts
Identifies all disabled computers - cannot authenticate, potential cleanup candidates.
Use Cases
- Find disabled accounts
- Identify decommissioned systems
- Cleanup candidates
- Temporary disable verification
Key Information
- Disabled computer accounts
- Cannot authenticate
- Potentially decommissioned
- Deletion candidates
- Inactive systems
Disabled Workstations
Shows only disabled workstation computers - inactive user devices.
Use Cases
- Inactive endpoint identification
- Retired workstation tracking
- Desktop cleanup candidates
- Temporary disable audit
Key Information
- Disabled workstations only
- Inactive user devices
- Retired desktops/laptops
- Potential cleanup
- Non-production endpoints
Disabled Servers
Lists only disabled servers - inactive infrastructure or decommissioned systems.
Use Cases
- Decommissioned server tracking
- Inactive infrastructure identification
- Server cleanup candidates
- Temporary disable verification
Key Information
- Disabled servers only
- Inactive infrastructure
- Decommissioned systems
- Potential deletion
- Non-production servers
Computers Created During Last XX Days
Tracks recently created computer accounts - monitor new device additions.
Use Cases
- Monitor new device joins
- Track infrastructure growth
- Audit computer creation
- New deployment verification
Key Information
- Recently created computers
- Creation timestamps
- Created by (admin)
- Initial OU placement
- Growth patterns
Computers Created Between Specified Dates
Historical analysis of computer creation within date range - track infrastructure growth patterns.
Use Cases
- Historical growth analysis
- Project timeline correlation
- Deployment campaign tracking
- Infrastructure expansion metrics
Key Information
- Computers created in date range
- Creation distribution over time
- Volume metrics
- Deployment patterns
- Infrastructure evolution
Computers Changed During Last XX Days
Tracks recently modified computer accounts - monitor configuration changes and updates.
Use Cases
- Monitor computer modifications
- Audit recent changes
- Security incident investigation
- Change management tracking
Key Information
- Recently modified computers
- Change timestamps
- Modified by (admin)
- Change types
- Activity patterns
Computers Changed Between Specified Dates
Historical view of computer modifications for compliance and incident correlation.
Use Cases
- Historical change analysis
- Compliance period auditing
- Incident time correlation
- Change frequency metrics
Key Information
- Changes within date range
- Modification distribution
- Change volume metrics
- Activity correlation
- Trend analysis
Deleted Computers
Shows deleted computer accounts in tombstone - can be restored if AD Recycle Bin enabled.
Use Cases
- Audit deleted computers
- Accidental deletion recovery
- Tombstone management
- Decommission tracking
Key Information
- Deleted computer names
- Deletion timestamps
- Tombstone expiration
- Restore capability
- Original OU location
Deleted Computers During Last XX Days
Recently deleted computers - critical for catching accidental deletions early.
Use Cases
- Monitor recent deletions
- Catch accidental deletions
- Audit deletion approval
- Quick recovery identification
Key Information
- Recently deleted computers
- Deletion dates
- Deleted by (admin)
- Time remaining for restore
- Decommission justification
Deleted Computers Between Specified Dates
Historical view of computer deletions for compliance reporting and decommission tracking.
Use Cases
- Historical deletion analysis
- Compliance reporting
- Decommission campaign tracking
- Cleanup effectiveness metrics
Key Information
- Deletions within date range
- Deletion distribution
- Volume metrics
- Decommission patterns
- Historical trends
Related Reports
Explore other computer report categories: