Logon Status Reports
12 ReportsAbout Logon Status Reports
Logon Status Reports track user authentication activity across your Active Directory environment. Monitor last logon times, identify inactive accounts, and analyze user activity patterns. Since lastLogon is not replicated, these reports scan all domain controllers to provide accurate data.
Monitor user logon patterns and activity
Identify stale and unused accounts
Analyze authentication trends
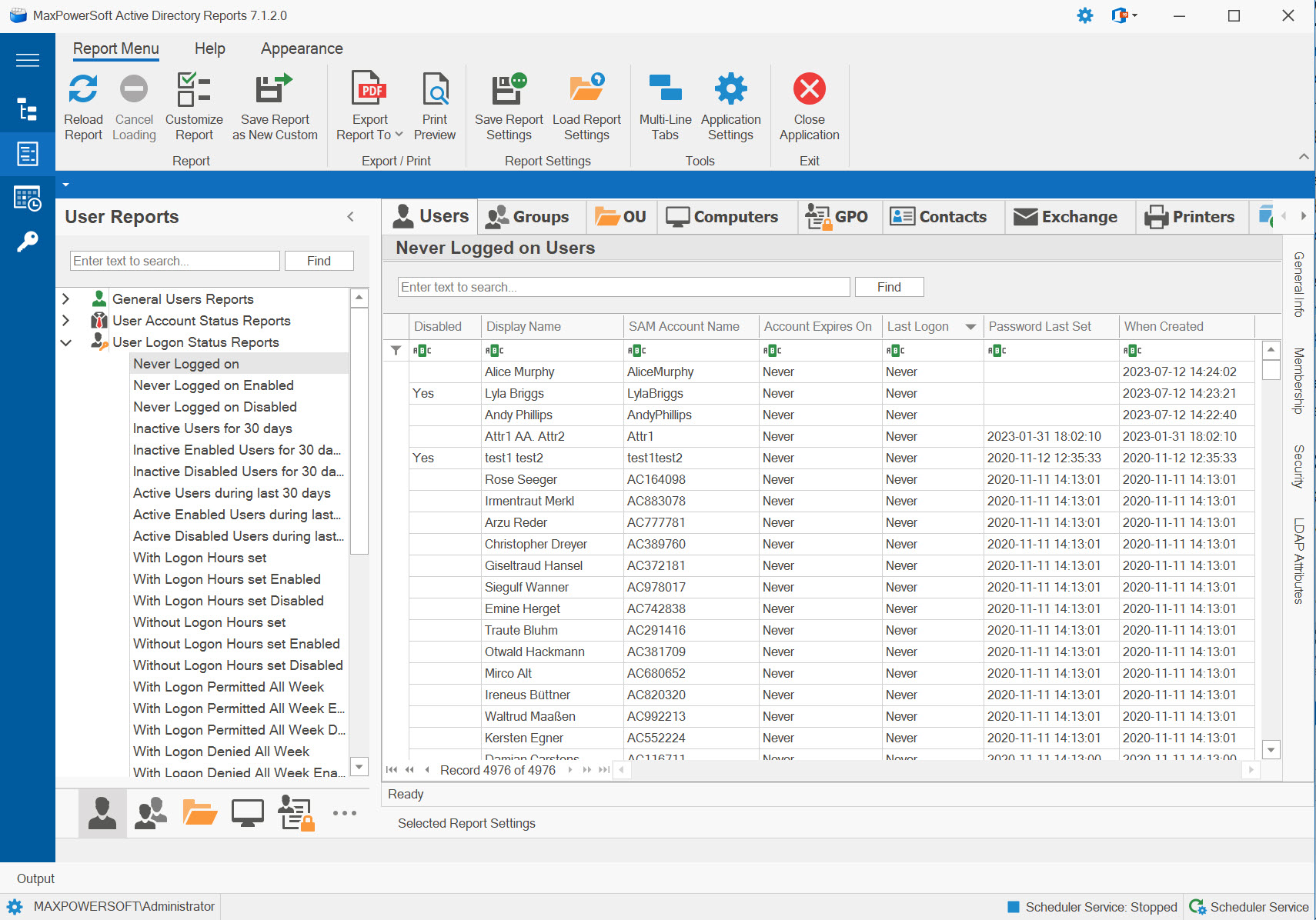
Example: Logon Status Reports in AD Reports
Available Reports
Never Logged on Users
Identifies all user accounts that have never authenticated to the domain, regardless of enabled/disabled status. Scans all domain controllers to ensure accuracy since lastLogon is not replicated.
Use Cases
- Identify unused accounts created but never used
- Clean up pre-created accounts
- Verify onboarding process completion
- Security audit for orphaned accounts
Key Information
- Account names never logged on
- Account creation date
- Account enabled/disabled status
- Days since creation
- Manager and department info
Never Logged on Enabled Users
Shows enabled accounts that have never been used to log on. These represent active security risks as they're enabled but potentially unmonitored.
Use Cases
- Identify security risks from unused enabled accounts
- Follow up on incomplete onboarding
- Disable or delete abandoned accounts
- Compliance cleanup for inactive access
Key Information
- Enabled accounts never used
- Account age since creation
- Associated user details
- Group memberships
- Provisioning date
Never Logged on Disabled Users
Lists disabled accounts that were never used before being disabled. Safe candidates for deletion.
Use Cases
- Identify accounts safe for deletion
- Clean up cancelled hires
- Remove abandoned pre-created accounts
- Database cleanup and optimization
Key Information
- Disabled unused accounts
- Creation and disable dates
- Reason for pre-creation
- Account metadata
- Deletion candidates
Inactive Users for XX Days
Shows users who haven't logged on for a customizable number of days. Critical for identifying stale accounts and unused licenses.
Use Cases
- Identify inactive accounts for review
- License reclamation opportunities
- Compliance with inactive account policies
- Security posture improvement
Key Information
- Last logon timestamp
- Days since last activity
- Account status
- User department and manager
- Inactivity threshold
Inactive Enabled Users for XX Days
Enabled accounts with no recent activity - highest priority for security review and potential disablement.
Use Cases
- Priority accounts for disabling
- Active security risk mitigation
- Follow up with managers on user status
- Automated disablement workflows
Key Information
- Enabled but inactive accounts
- Last authentication date
- Inactivity duration
- Group memberships and privileges
- Manager contact info
Inactive Disabled Users for XX Days
Disabled accounts with no recent activity before disablement. Candidates for permanent deletion.
Use Cases
- Identify accounts ready for deletion
- Clean up long-disabled accounts
- Audit terminated employee processing
- Database optimization
Key Information
- Disabled inactive accounts
- Last activity before disable
- Time disabled
- Termination details
- Deletion eligibility
Active Users During Last XX Days
Shows users who have authenticated within the specified timeframe. Useful for activity analysis and license utilization.
Use Cases
- Verify active user population
- License utilization analysis
- Activity trending and metrics
- Validate access patterns
Key Information
- Recent logon activity
- Last authentication timestamp
- Activity within timeframe
- User details and status
- Usage patterns
Active Enabled Users During Last XX Days
Enabled accounts with recent activity - your actively utilized user base.
Use Cases
- True active user count
- License assignment validation
- User engagement metrics
- Baseline for normal activity
Key Information
- Active enabled population
- Recent logon times
- Authentication frequency
- Department distribution
- Usage statistics
Active Disabled Users During Last XX Days
Shows disabled accounts that had activity before being disabled - useful for audit trailing.
Use Cases
- Audit recently disabled accounts
- Verify termination processing timing
- Last activity before disablement
- Offboarding quality control
Key Information
- Last activity date
- Disable timestamp
- Activity before termination
- Disabled by administrator
- Termination workflow status
Logon with Smart Card Required
Lists accounts configured to require smart card authentication - high-security accounts.
Use Cases
- Audit smart card requirements
- Verify high-security account settings
- Compliance with MFA policies
- Track PIV/CAC authentication
Key Information
- Smart card required accounts
- Certificate information
- Account privilege levels
- Authentication policy
- Compliance status
MNS Logon Accounts
Shows accounts with MNS (Microsoft Namespace) logon capabilities for special authentication scenarios.
Use Cases
- Audit MNS logon permissions
- Service account identification
- Special authentication tracking
- Cross-domain access review
Key Information
- MNS logon configured accounts
- Authentication methods
- Service associations
- UPN suffixes
- Cross-domain capabilities
Last Logon Timestamp
Shows lastLogonTimestamp attribute which IS replicated (unlike lastLogon) but updated less frequently - useful for approximate activity tracking.
Use Cases
- Quick approximate activity check
- Faster reporting without DC scans
- Historical activity trends
- Bulk analysis of account usage
Key Information
- Replicated timestamp attribute
- Updated every 14 days by default
- Approximate last logon time
- No DC scanning required
- Faster query performance
Related Reports
Explore other user report categories:
See These Reports in Action
Try AD Reports free for 14 days — run any of these reports on your own Active Directory.
Download Free Trial View All Features