Active Directory Users
Active Directory Users are individual accounts that represent people or entities with access to resources within an Active Directory domain. In an Active Directory environment, user accounts play a critical role in network security, authentication, and access control. Each user account contains essential information such as the user's name, username (often referred to as the User Principal Name or UPN), password, contact details, group memberships, and other attributes.
Active Directory users serve as security principals, which means they can be granted permissions and access rights to various network resources, such as files, folders, printers, and applications. User accounts are used for authentication purposes, allowing users to log in to the network and access resources based on their assigned permissions.
Administrators can manage Active Directory users by creating, modifying, and disabling accounts as needed. User accounts can be organized into Organizational Units (OUs) to simplify management and policy application. OUs provide a way to apply specific settings and configurations to groups of users with similar roles or requirements.
Overall, Active Directory users are at the core of network interaction, enabling individuals to utilize resources within the domain and facilitating the secure and efficient management of a Windows-based network environment.
General User Reports
Within the "General Users Report" section of AD Reports, you will find a comprehensive range of reports focusing on general user information. The reports available in this section include:
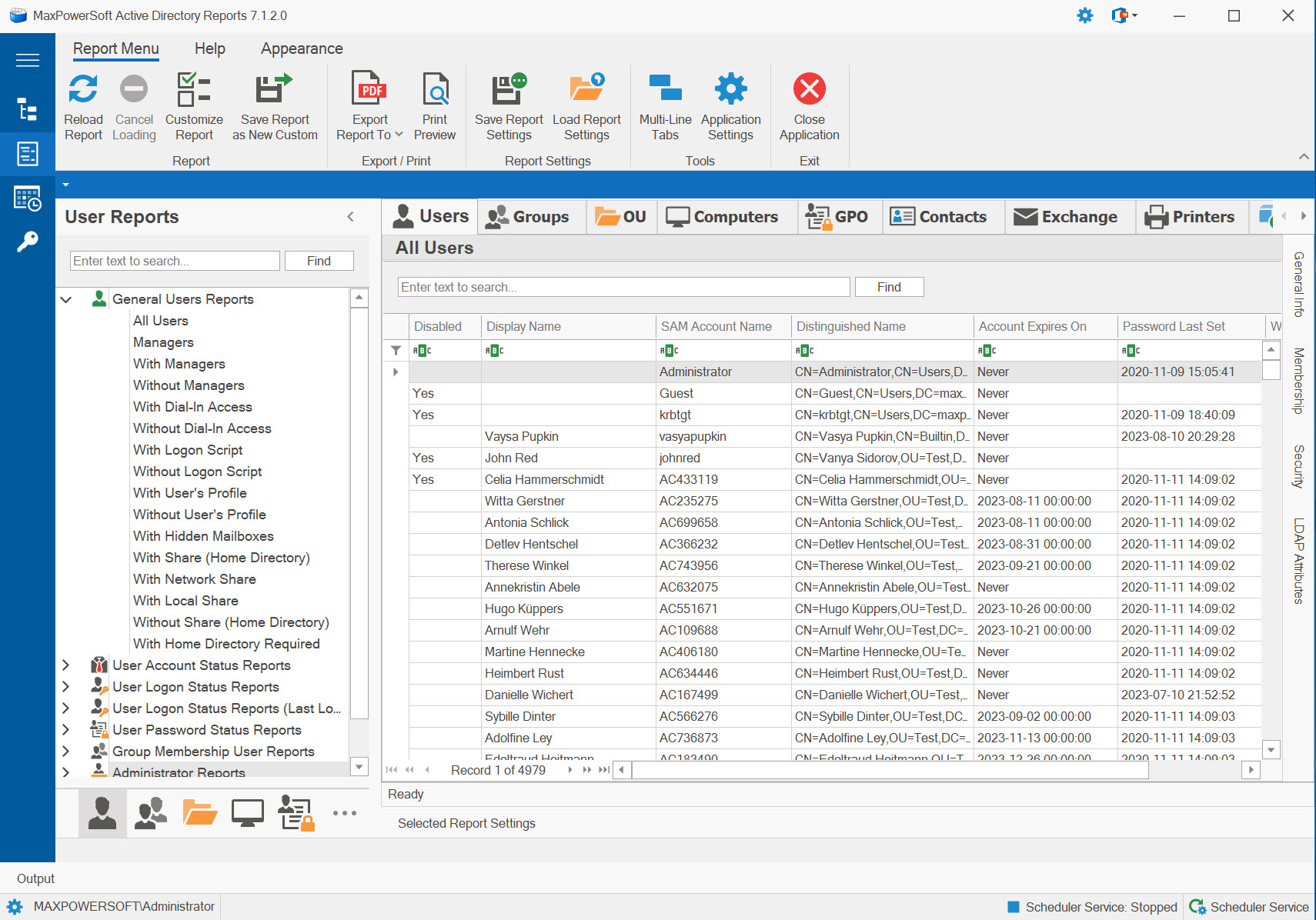
All Users Report
The "All Users" report retrieves all user security principals in a selected domain, excluding contacts, without the application of any additional LDAP filters.
With Managers Report
The "With Managers" user report generates a list of users who have a direct reporting relationship to a particular user (manager).
Without Managers Report
The "Without Managers" report is essentially the opposite of the "With Managers" report. It provides a list of users who do not have any assigned manager or do not report to any specific user. In other words, it identifies users who are not under the direct supervision of any manager within the specified domain.
With Dial-In Access Report
The "With Dial-In Access" user report compiles a list of users with permission to remotely connect to the corporate network via the Remote Access Service from outside the corporate network.
Without Dial-In Access Report
The "Without Dial-In Access" user report returns a list of users who do not have permission to establish a dial-in connection to the Remote Access Service from outside the corporate network.
With Logon Script Report
The "With Logon Script" report provides a list of users who have specified a specific path for their logon script.
Without Logon Script Report
The "Without Logon Script" report compiles a list of users who have not specified any path for their logon script.
With User's Profile
The "With User's Profile" user report generates a list of users who have a specified location for their user profiles.
Without User's Profile
The "Without User's Profile" user report compiles a list of users who do not have a specified location for their user profiles.
With Hidden Mailboxes
The "With Hidden Mailboxes" user report presents a list of users whose mailboxes are configured to be hidden from the Global Address List (GAL).
With Share (Home Directory)
The user report for "With Share (Home Directory)" provides a list of users who have designated their home directory as the location (local or network) to store their personal files. By enabling centralized storage, users gain the ability to access their files from any computer connected to the network. This convenient feature facilitates easy backup and recovery of network files for IT administrators.
With Network Share
The "With Network Share" user report returns a list of users with designated their home directory as the network location for storing their personal files.
With Local Share
The user report "With Local Share" generates a list of users with designated their home directory as the local location for storing their personal files.
Without Share (Home Directory)
The user report "Without Share (Home Directory)" provides a list of users without any designated specific sharing or storage location for their personal files.