General GPO Reports
18 ReportsAbout General GPO Reports
General Group Policy Object Reports provide comprehensive insights into GPO configuration, linkages, and lifecycle. Track enabled/disabled settings, link status, creation, modifications, and deletions. Essential for maintaining effective Group Policy deployment and troubleshooting policy issues.
Track enabled/disabled
Monitor GPO deployment
Track changes and history
About Group Policy Objects
GPOs are containers for configuration settings applied to users and computers:
- User Settings: Apply to users regardless of computer
- Computer Settings: Apply to computers regardless of user
- Linkage: Must be linked to sites, domains, or OUs to take effect
- Processing Order: Local → Site → Domain → OU (LSDOU)
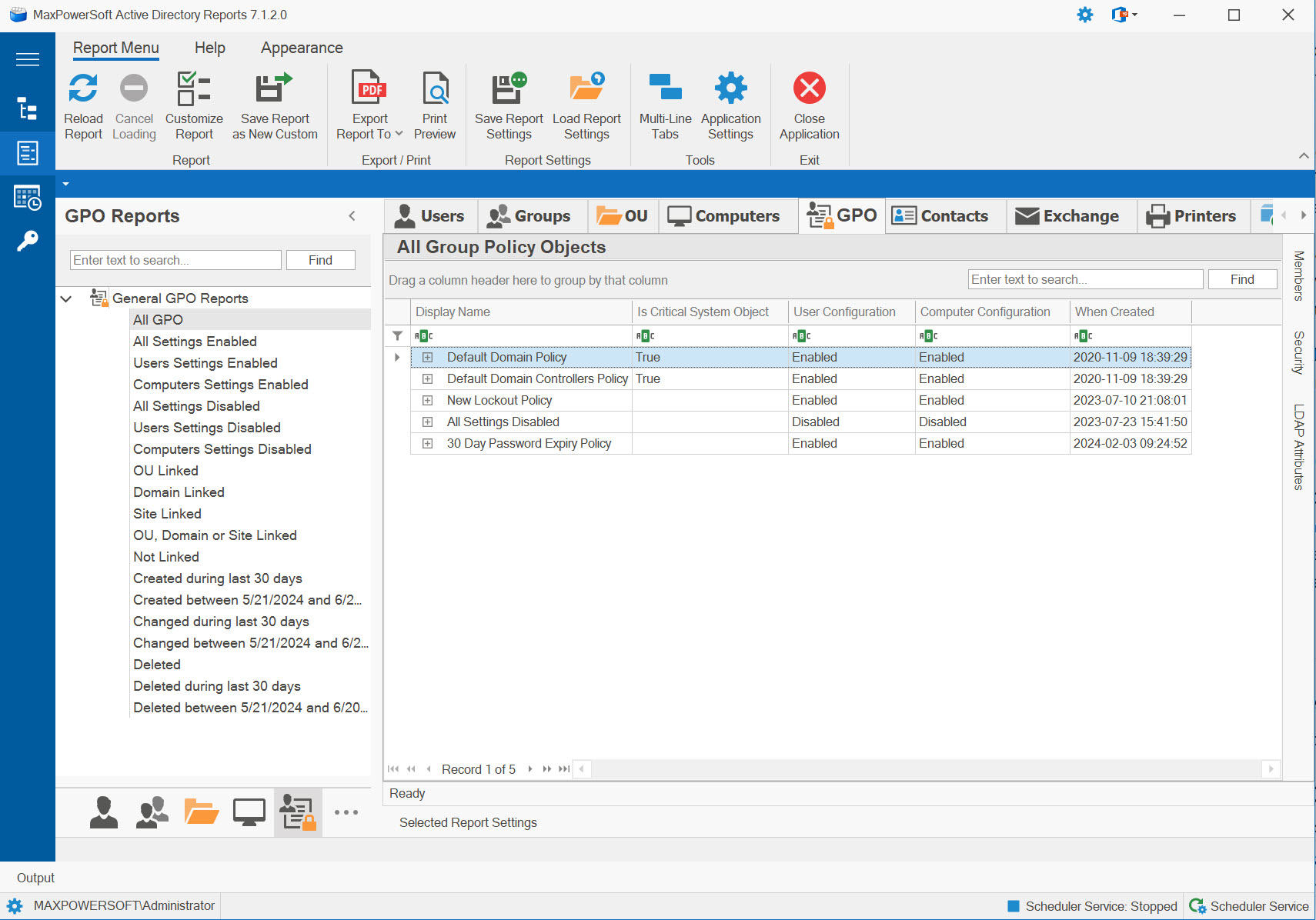
Example: General GPO Reports
Available Reports
All Group Policy Objects
Comprehensive inventory of all GPOs in the domain - complete list regardless of link status or settings.
Use Cases
- Complete GPO inventory
- Total GPO count
- GPO naming audit
- Baseline for other reports
Key Information
- All domain GPOs
- GPO names and GUIDs
- Creation/modification dates
- Link status
- Settings status (enabled/disabled)
All Settings Enabled GPOs
Shows GPOs with both User and Computer settings enabled - fully active policies.
Use Cases
- Identify fully active GPOs
- Audit complete policy deployment
- Performance optimization baseline
- Standard GPO configuration
Key Information
- GPOs with all settings on
- Both user & computer active
- Maximum policy impact
- Processing time considerations
- Complete functionality
Users Settings Enabled GPOs
Lists GPOs with User settings enabled - applies user-specific configurations.
Use Cases
- Audit user policy deployment
- User-specific GPO tracking
- User logon performance analysis
- Policy application verification
Key Information
- GPOs processing user settings
- User configuration enabled
- Computer settings may be disabled
- User logon processing
- User-focused policies
Computers Settings Enabled GPOs
Shows GPOs with Computer settings enabled - applies machine-specific configurations.
Use Cases
- Audit computer policy deployment
- Machine-specific GPO tracking
- Startup performance analysis
- Device configuration verification
Key Information
- GPOs processing computer settings
- Computer configuration enabled
- User settings may be disabled
- Computer startup processing
- Machine-focused policies
All Settings Disabled GPOs
Identifies GPOs with both User and Computer settings disabled - inactive policies.
Use Cases
- Find completely disabled GPOs
- Identify cleanup candidates
- Audit unused policies
- Testing/staging GPOs
Key Information
- Completely inactive GPOs
- No processing impact
- Potential deletion candidates
- Temporary test GPOs
- Archived policies
Users Settings Disabled GPOs
Shows GPOs with User settings disabled - computer-only policies or optimization.
Use Cases
- Computer-only GPOs
- Performance optimization verification
- Intentional user setting exclusion
- Machine-focused policies
Key Information
- GPOs with user portion disabled
- Computer settings may be enabled
- Faster user logon processing
- Optimization technique
- Computer-only scope
Computers Settings Disabled GPOs
Lists GPOs with Computer settings disabled - user-only policies or optimization.
Use Cases
- User-only GPOs
- Performance optimization verification
- Intentional computer setting exclusion
- User-focused policies
Key Information
- GPOs with computer portion disabled
- User settings may be enabled
- Faster computer startup processing
- Optimization technique
- User-only scope
OU Linked GPOs
Shows GPOs linked to Organizational Units - most common GPO deployment method.
Use Cases
- Standard GPO deployment audit
- OU-specific policy tracking
- Departmental policy verification
- Most granular policy control
Key Information
- GPOs linked to OUs
- Target OU paths
- Link order and precedence
- Enforced link status
- Most common deployment
Domain Linked GPOs
Lists GPOs linked at domain level - applies to entire domain.
Use Cases
- Domain-wide policy audit
- Organization-wide settings
- Default security policies
- Universal configurations
Key Information
- Domain-level GPO links
- Affects all domain objects
- Can be blocked by OUs
- Higher precedence than site
- Organization-wide scope
Site Linked GPOs
Shows GPOs linked to AD Sites - location-specific policies.
Use Cases
- Location-specific policies
- Network-based configurations
- Printer and resource deployment
- Multi-site organizations
Key Information
- Site-level GPO links
- Physical location based
- Lowest processing precedence
- Cross-domain capabilities
- Network-specific settings
OU, Domain, or Site Linked GPOs
Lists all GPOs with any linkage - excludes unlinked/orphaned policies.
Use Cases
- Identify active GPOs
- Exclude orphaned policies
- Deployment verification
- Active policy inventory
Key Information
- All linked GPOs
- Any link type (OU/domain/site)
- Actively deployed policies
- Excludes orphans
- Production GPOs
Not Linked GPOs
Identifies unlinked/orphaned GPOs - not applied anywhere, potential cleanup candidates.
Use Cases
- Find orphaned GPOs
- Identify unused policies
- Cleanup candidates
- Test/development GPOs
Key Information
- Unlinked GPOs
- Not applied anywhere
- Zero policy impact
- Possible orphans
- Test or backup GPOs
GPOs Created During Last XX Days
Tracks recently created GPOs - monitor new policy deployment and changes.
Use Cases
- Monitor recent GPO creation
- Audit new policy approval
- Track policy changes
- New project identification
Key Information
- Recently created GPOs
- Creation timestamps
- Created by (admin)
- Initial configuration
- Growth trends
GPOs Created Between Specified Dates
Historical analysis of GPO creation within date range for compliance reporting.
Use Cases
- Historical creation analysis
- Compliance period reporting
- Project timeline correlation
- Growth pattern analysis
Key Information
- GPOs created in date range
- Creation distribution over time
- Volume metrics
- Policy evolution
- Trend identification
GPOs Changed During Last XX Days
Tracks recently modified GPOs - essential for change management and troubleshooting.
Use Cases
- Monitor GPO modifications
- Audit recent changes
- Troubleshoot recent issues
- Change management tracking
Key Information
- Recently modified GPOs
- Change timestamps
- Modified by (admin)
- Change types
- Activity patterns
GPOs Changed Between Specified Dates
Historical view of GPO modifications for compliance auditing and issue correlation.
Use Cases
- Historical change analysis
- Compliance period auditing
- Incident time correlation
- Change frequency metrics
Key Information
- Changes within date range
- Modification distribution
- Change volume metrics
- Activity correlation
- Trend analysis
Deleted GPOs
Shows deleted GPOs in tombstone - can be restored if AD Recycle Bin is enabled.
Use Cases
- Audit deleted GPOs
- Accidental deletion recovery
- Tombstone management
- Deletion pattern analysis
Key Information
- Deleted GPO names
- Deletion timestamps
- Tombstone expiration
- Restore capability
- Original settings (if Recycle Bin)
Deleted GPOs During Last XX Days
Recently deleted GPOs - critical for catching accidental deletions early.
Use Cases
- Monitor recent deletions
- Catch accidental deletions
- Audit deletion approval
- Quick recovery identification
Key Information
- Recently deleted GPOs
- Deletion dates
- Deleted by (admin)
- Time remaining for restore
- Deletion justification
- Naming Convention: Use clear, descriptive names (e.g., "Security-Workstations-Baseline")
- Disable Unused Sides: If User or Computer settings are empty, disable that side for faster processing
- Link at OU Level: OU-linked GPOs provide the most flexible control
- Document GPOs: Always add description explaining purpose and owner
- Avoid Conflicts: Use "No Override" (Enforced) and "Block Inheritance" sparingly
- Test First: Test GPOs in lab before production deployment
- Clean Up: Regularly delete unused and unlinked GPOs
Related Reports
Explore other GPO and OU report categories:
See These Reports in Action
Try AD Reports free for 14 days — run any of these reports on your own Active Directory.
Download Free Trial View All Features