Computer Logon Status Reports
9 ReportsAbout Computer Logon Status Reports
Computer Logon Status Reports provide critical insights into computer activity and usage patterns. Track computers that have never logged on, identify inactive systems, and find actively used devices. Essential for cleanup campaigns, license optimization, and security auditing.
Find unused computers
Identify stale accounts
Track usage patterns
About lastLogon Attribute
Important: The lastLogon attribute is NOT replicated between domain controllers!
- Multi-DC Scanning: These reports scan ALL domain controllers to get accurate data
- Processing Time: May take longer than other reports due to multiple DC queries
- Accuracy: Ensures you get the true last logon across entire domain
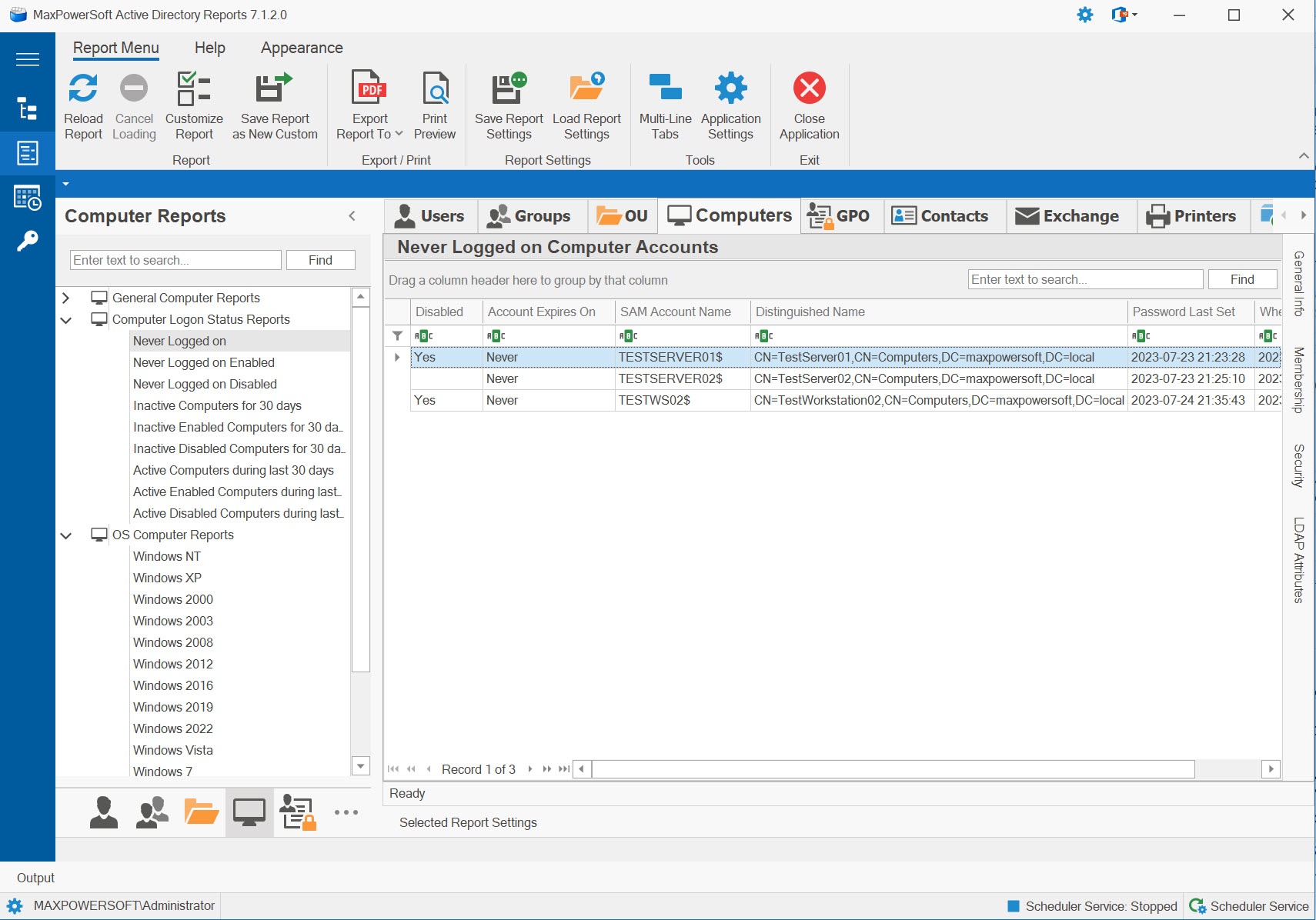
Example: Computer Logon Status Reports
Available Reports
Never Logged On Computers
Lists ALL computers (enabled and disabled) that have never authenticated to the domain - potential cleanup candidates.
Use Cases
- Find pre-staged but unused computers
- Identify failed deployments
- Cleanup campaign planning
- Asset tracking verification
Key Information
- Computers with no logon history
- Both enabled and disabled
- Never used systems
- Creation dates
- Deletion candidates
Never Logged On Enabled Computers
Shows ENABLED computers that have never logged on - active security risk, immediate attention needed.
Use Cases
- Security audit for unused active accounts
- Failed deployment identification
- Immediate cleanup priorities
- Risk assessment
Key Information
- Enabled but never used
- Active security exposure
- Can authenticate (but hasn't)
- Potential attack vector
- High priority cleanup
Never Logged On Disabled Computers
Lists DISABLED computers that never logged on - safe to delete, already neutralized.
Use Cases
- Safe deletion candidates
- Cleanup without risk
- Failed pre-stage tracking
- AD hygiene improvement
Key Information
- Disabled AND never used
- No security risk
- Safe to delete immediately
- Cleanup opportunities
- AD clutter reduction
Inactive Computers for XX Days
ALL computers (enabled and disabled) inactive for specified days - stale accounts needing review.
Use Cases
- Stale account identification
- Cleanup campaign planning
- License optimization
- Inactive device audit
Key Information
- No logon for X days
- Both enabled and disabled
- Last logon timestamps
- Inactivity duration
- Potential cleanup targets
Inactive Enabled Computers for XX Days
ENABLED computers inactive for specified days - security risk, should be disabled or investigated.
Use Cases
- Security risk identification
- Disable candidate prioritization
- Unused but active accounts
- Immediate action targets
Key Information
- Enabled but inactive
- Can authenticate (security risk)
- Unused for X days
- Disable candidates
- Investigation needed
Inactive Disabled Computers for XX Days
DISABLED computers inactive for specified days - safe to delete after retention period.
Use Cases
- Safe deletion candidates
- Verify retention periods met
- Final cleanup phase
- AD hygiene maintenance
Key Information
- Disabled AND inactive
- No security risk
- Retention period verification
- Ready for deletion
- Cleanup opportunities
Active Computers During Last XX Days
ALL computers (enabled and disabled) that logged on at least once during specified period - actively used systems.
Use Cases
- Active device inventory
- Usage pattern analysis
- License planning (active systems)
- Production system identification
Key Information
- Recently active computers
- Last logon within X days
- Usage confirmation
- Active device count
- Production systems
Active Enabled Computers During Last XX Days
ENABLED computers that logged on during specified period - healthy, properly functioning systems.
Use Cases
- Production system inventory
- Healthy system baseline
- Active endpoint count
- Normal operation verification
Key Information
- Enabled AND recently active
- Properly functioning
- Production systems
- Healthy account baseline
- Normal operation
Active Disabled Computers During Last XX Days
DISABLED computers that somehow logged on recently - unusual situation requiring investigation!
Use Cases
- Anomaly detection
- Recently disabled systems
- Disable timing verification
- Investigation candidates
Key Information
- Disabled but recently active
- Unusual situation
- Recently disabled systems
- Timing considerations
- Investigation needed
Recommended Cleanup Process:
- Phase 1 - Safe Deletion: Delete "Never Logged On Disabled" and "Inactive Disabled for 180+ days"
- Phase 2 - Disable Active Risks: Disable "Never Logged On Enabled" and "Inactive Enabled for 90+ days"
- Phase 3 - Wait Period: Wait 30 days to verify no complaints or issues
- Phase 4 - Final Cleanup: Delete accounts disabled in Phase 2 after retention period
- Ongoing: Run monthly to maintain clean AD environment
Related Reports
Explore other computer report categories: