Computer Kerberos Configuration Reports
3 ReportsAbout Computer Kerberos Configuration Reports
Computer Kerberos Configuration Reports audit Kerberos delegation settings on computer accounts. These reports identify computers configured for constrained delegation, protocol transition (S4U2Self), and resource-based constrained delegation — critical for multi-tier application security and attack surface management.
Audit constrained delegation
S4U2Self configuration
Resource-based delegation
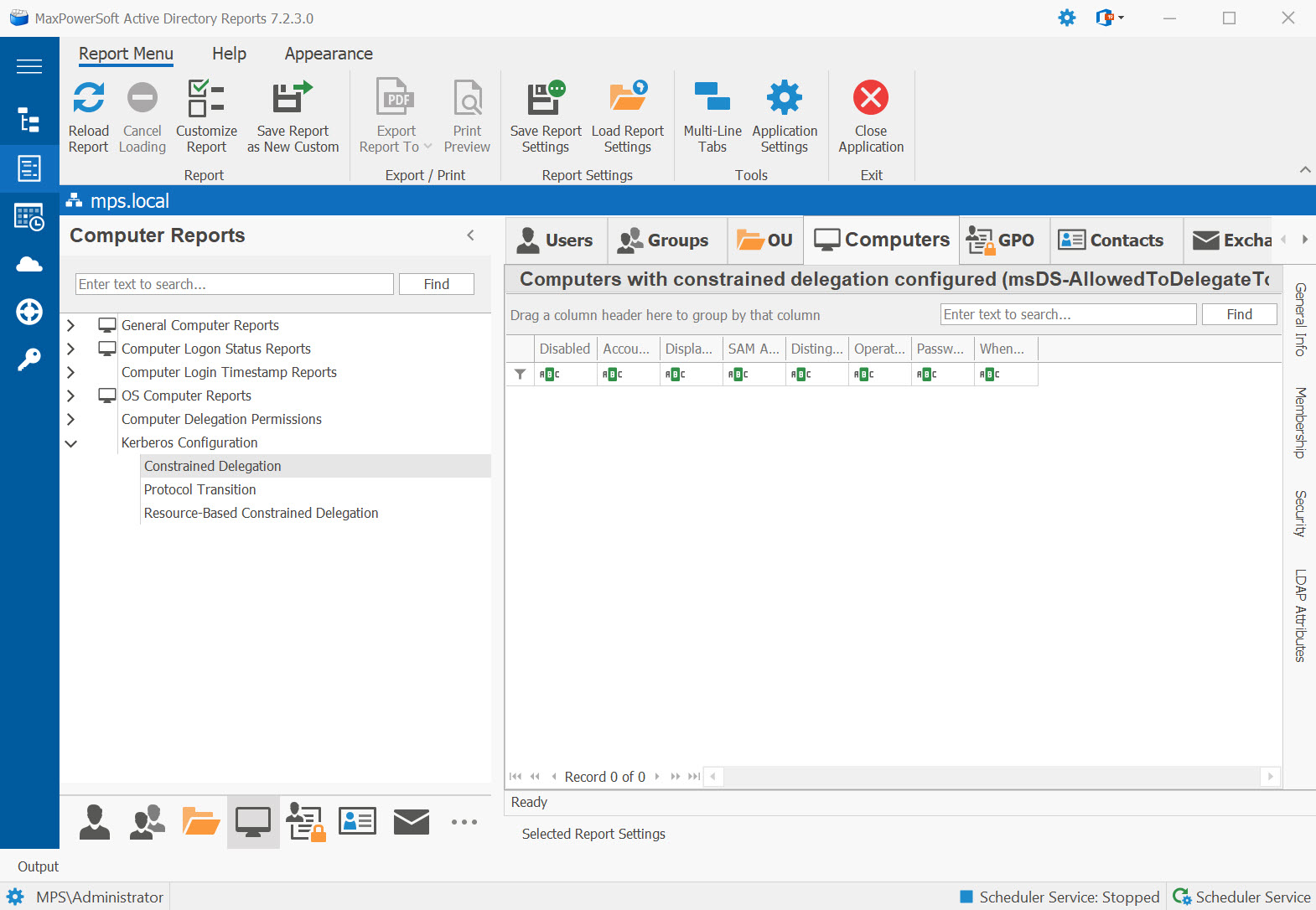
Example: Computer Kerberos Configuration Reports in AD Reports
Available Reports
Constrained Delegation
Computers with constrained delegation configured (msDS-AllowedToDelegateTo). These computers
can impersonate users to specific services listed in their delegation configuration.
Use Cases
- Identify computers impersonating users for backend services (IIS, SQL, Exchange)
- Verify delegation scope is appropriately restricted
- Audit multi-tier application server configurations
Key Information
- Computer name and Distinguished Name
- Allowed delegation targets (msDS-AllowedToDelegateTo)
- Operating System and OU path
Protocol Transition
Computers with Kerberos protocol transition enabled (S4U2Self). These computers can request service tickets on behalf of users even when the initial authentication did not use Kerberos.
Use Cases
- Find computers with S4U2Self enabled (TrustedToAuthForDelegation)
- Audit computers that can generate service tickets without a Kerberos TGT
- Highest-risk delegation category for computers
Key Information
- Computer name and Distinguished Name
- TrustedToAuthForDelegation attribute (true/false)
- Delegation targets if constrained
- OU path and Operating System
Resource-Based Constrained Delegation
Computers with Resource-Based Constrained Delegation (msDS-AllowedToActOnBehalfOfOtherIdentity).
RBCD allows the target computer to specify which accounts can delegate to it, without requiring
Domain Admin privileges to configure.
Use Cases
- Audit computers that allow specific accounts to delegate to them via RBCD
- Identify non-standard RBCD configurations indicating possible compromise
- Post-incident investigation support
Key Information
- Computer name and Distinguished Name
- Accounts allowed to act on its behalf
- Whether entries are expected service accounts or anomalous
See These Reports in Action
Try AD Reports free for 14 days — run any of these reports on your own Active Directory.
Download Free Trial View All Features