GPO Delegation Permissions Reports
4 ReportsAbout GPO Delegation Permissions Reports
GPO Delegation Permissions Reports audit the security permissions assigned to Group Policy Objects. Review who has been granted access to edit, delete, or manage GPOs — essential for ensuring only authorized administrators can modify policies that affect your entire domain.
Audit GPO access rights
Inherited vs explicit rights
Find over-privileged accounts
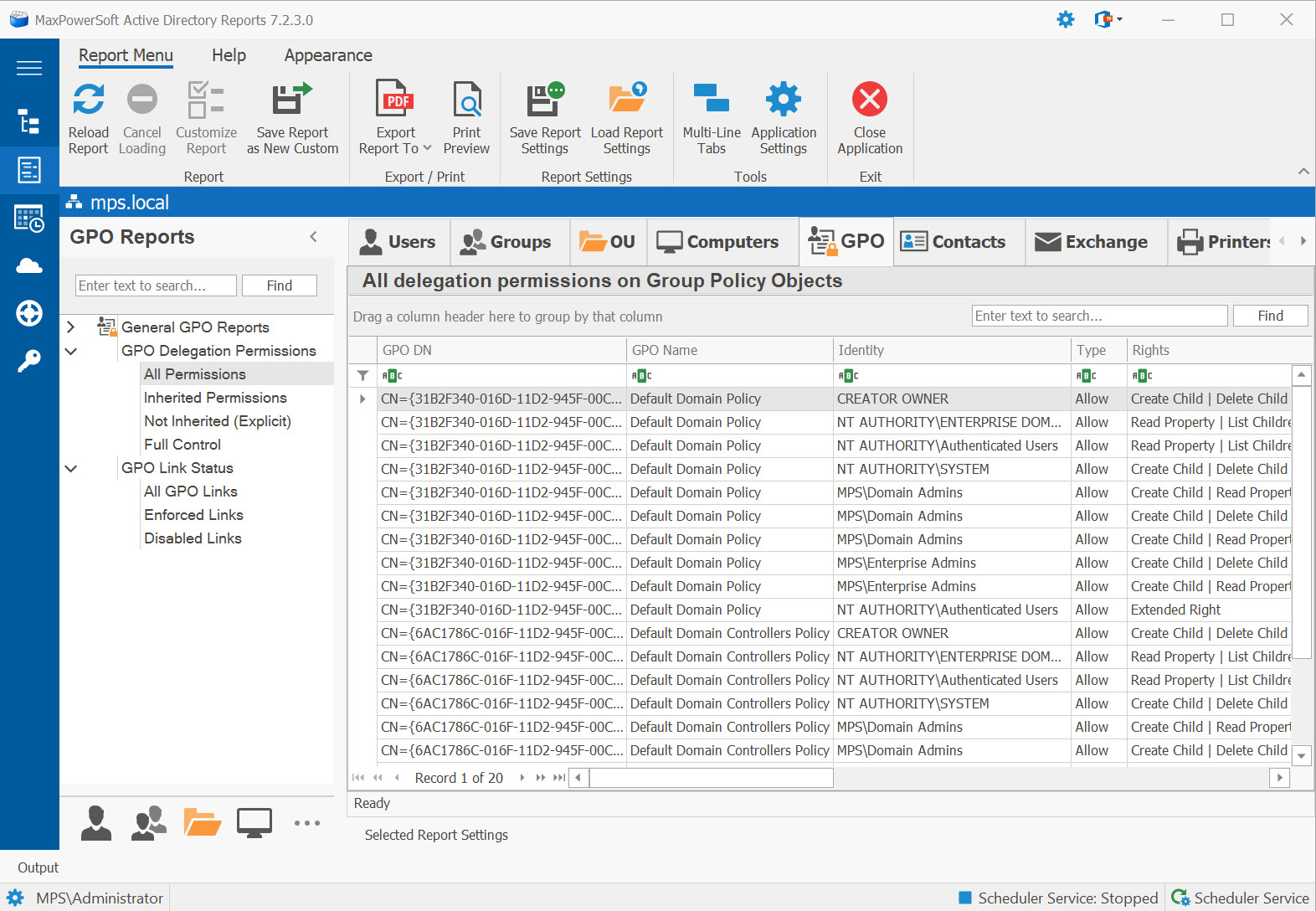
Example: GPO Delegation Permissions Reports in AD Reports
Available Reports
All Permissions
All delegation permissions on Group Policy Objects. Provides a comprehensive view of every permission entry on GPOs, combining inherited and explicitly set permissions.
Use Cases
- Audit who can edit or link Group Policy Objects
- Identify unauthorized GPO management access
- AD security hardening and SOX / CIS compliance reviews
- GPO review before domain migrations
Key Information
- GPO Name and GUID
- Trustee account or group
- Permission type (read/edit/full)
- Inheritance flag
Inherited Permissions
Inherited delegation permissions on Group Policy Objects. Shows permissions that flow down from parent containers via the AD inheritance model.
Use Cases
- Understand default permissions inherited from the domain level
- Verify expected GPO management access
- Identify GPOs where domain-wide delegations may grant unexpected edit rights
Key Information
- Source container (origin of the inherited permission)
- Trustee account or group
- Permission type
- Propagation scope
Not Inherited (Explicit)
Explicitly set delegation permissions on Group Policy Objects. These are intentional permission assignments made directly on GPO objects.
Use Cases
- Track custom GPO management delegations
- Detect accounts granted direct GPO edit rights
- Identify who was manually granted access to specific GPOs
Key Information
- Trustee account or group
- Explicit permission type
- GPO name and Distinguished Name
- Delegation scope
Full Control
Full Control delegation permissions on Group Policy Objects. Identifies accounts with complete control over GPOs, including the ability to modify settings, delete, and change permissions.
Use Cases
- Identify accounts that can edit, delete, and link any GPO
- Detect unauthorized GPO management (highest risk category)
- Tier 0 audit — includes policies that affect domain controllers
- Restrict to dedicated Group Policy administrators
Key Information
- Trustee account name and type
- GPO name and GUID
- GPO links (which OUs / sites it affects)
- Inheritance flag
See These Reports in Action
Try AD Reports free for 14 days — run any of these reports on your own Active Directory.
Download Free Trial View All Features